OpenID Connect identification
Identification in E-Ident can be done using the OIDC protocol and the implementation supports the Authorization Code Flow with the optional
PKCE and
CIBA flows. The figure below illustrates the identification sequence when using OIDC.
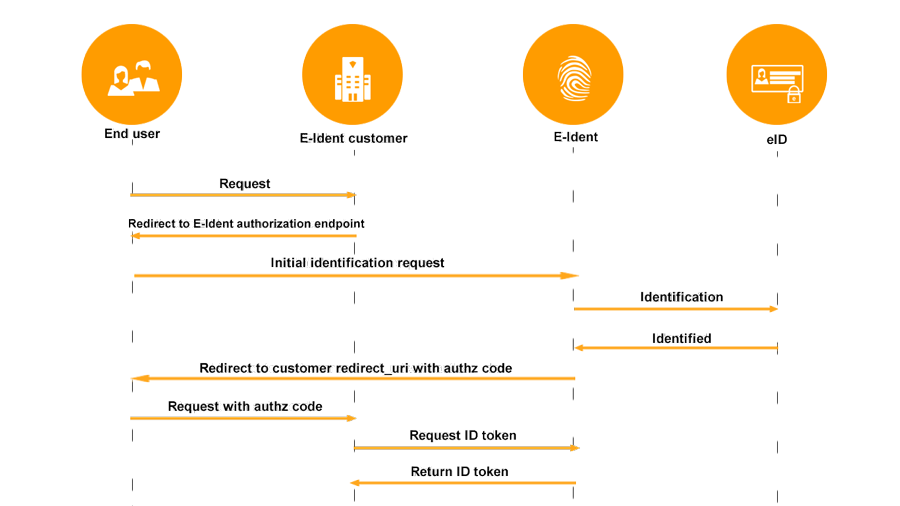
- The end user accesses the E-Ident customer site with a request to log on.
- The end user browser is redirected to E-Ident to begin identification. Sample identification request:
https://www.ident-preprod1.nets.eu/its/index.html?client_id=<client_id>&response_type=code&redirect_uri=<redirect_uri>&scope=openid+ssn&state=2017-06-12-15.12.43.345354&nonce=386145d332342
Read more about the mandatory and optional parameters. - End user identification is initiated towards a selected eID. The end user supplies his/her credentials.
- E-Ident redirects the end user to the E-Ident customer's
redirect_uri by appending the query string
?code=<authorization code>. Similarily, the
state parameter, as sent by the customer, is also appended to the
redirect_uri. - The E-Ident customer requests an
ID Token based on the authorization code. Successive token requests with the same authorization code (code) will result in error and invalidation of previously accessed tokens.
PKCE flow
The Proof Key for Code Exchange (PKCE) flow allows Single Page Application (SPA) and native apps to retrieve the ID token directly in a secure way without revealing the password and not through a backend call. The flow is optional and works likes this:
Customers must generate a
code_verifier value
Optionally the customers transforms the
code_verifier value and sends it as a
code_challenge to the E-Ident service along with the identification request. The customers may also optionally send the
code_challenge_method (SHA-256 or plain) along with the identification request.
After authentication, the
code_verifier is sent when retrieving the token. The E-Ident service will verify the
code_verifier against the original challenge, using the specified method (SHA-256 or plain).
CIBA flow
Standard authentication using OIDC relies on the user agent (user's browser) first access the OIDC provider to initiate the session. The response from the provider is a web UI that guides the user through the authentication sequence.
The Client Initiated Backchannel Authentication (CIBA) flow enables authentication sessions to be initiated and processed in a different channel than the browser through the E-Ident web UI.
The following diagram illustrates a CIBA flow use case:
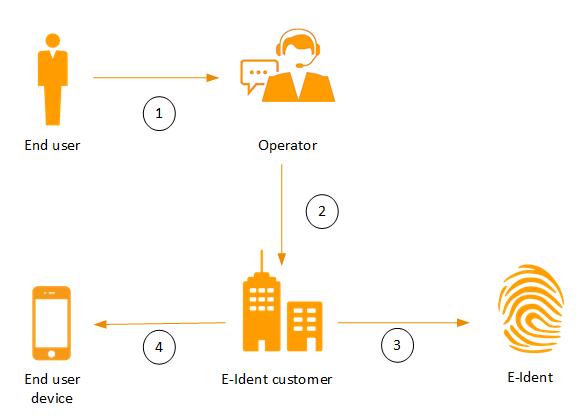
In this use case:
A user contacts an agent by phone or e-mail requesting for some service or assistance.
The request is forwarded to the back end system that requires the user to be remotely authenticated.
A CIBA request is sent to the E-Ident service to initiate authentication.
The user then completes the sequence by providing their consent (by authenticating using their device).
Another alternative would be for the user to request for a service through an app published by their provider (the company providing a service such as a bank, school, institution, etc.).
After authentication in the user device, the service provider in this use case can retrieve the ID token from the E-Ident service.
Implementation
To implement the backchannel flow, customers will need to follow the following sequence:
- call the CIBA endpoint to start a new authentication transaction.
See CIBA specific identification parameters.
- use the response to start user authentication (user consent)
- wait for the user complete(alternatively, poll the server for updates)
- retrieve the ID token
Requesting for a CIBA transaction
curl -kiSs \
https://www.ident-preprod1.nets.eu/oidc/ciba \
-H Authorization: Basic <<Base64Enocoded username:password>> \
-d scope=openid \
-d amr_values=id_verifier
Upon success, the server will respond with a unique ID that is bound to the new session
{"auth_req_id":"c69597e96f5a4dcc970ec38e5a85a4c3","interval":5,"expires_in":600}
The
auth_req_id is a session ID that can be provided to the authentication app to facilitate consent confirmation (authentication).
Requesting for CIBA transaction with login hint and binding message
When starting a CIBA transaction with Nets ID verifier, the following optional parameters ntdr-doc-types and ntdr-app-doclist can be sent through binding_message. ntdr-doc-types parameter accepts the following values: I, P, D and V. These alphabets mean ID cards, Passport booklets, Driver's license and Viza/crew credentials respectively. ntdr-app-doclist parameter accepts boolean value indicating whether the document type selection page will be shown to the user.
For Nets ID Verifier, binding_message will accept value in JSON format.
A valid JSON format for binding_message is:
{
"ntdr-doc-types": "<I, V, D, P>" (multiple values, with comma separation, are allowed),
"ntdr-app-doclist": "<true/false>"
}
BankID (NO)
When starting a CIBA transaction with Norwegian BankID, it's required to specify the end user's identity. This is done by passing the login_hint parameter with the correct data depending on the authentication method.
BankID (SE)
For BankID (SE), it's optional to specify login_hint. If login_hint is provided, then that will be used to exclude other user's SSN than the provided SSN.
The binding message will accept values in text or JSON format which will appear on the end user's device. BankID SE supports two ways of CIBA authentication depending on the amr_values parameter.
se_bankid
The “amr_values" can be passed as “se_bankid" which will return auth_req_id and autostart_token. Use this token to launch the app. Please refer
https://www.bankid.com/en/utvecklare/guider/teknisk-integrationsguide/programstart for technical details.
se_bankid:mobile
The “amr_values" can also be passed as “se_bankid:mobile" which will return one additional token called qr_data, use this qr_data to create animated QR code which can be scanned by BankID app. Once the first QR code is created then the polling should be done every second for token endpoint. The qr_data will be returned in every polling which can be used to update the animated QR code every second.
curl -kiSs \
https://www.ident-preprod1.nets.eu/oidc/ciba \
-H Authorization: Basic <<Base64Enocoded username:password>> \
-d scope=openid \
-d amr_values=se_bankid:mobile
Upon success, the server will respond with a unique ID and qr_data that is bound to the new session-
{
"auth_req_id": "5be667afc6624d938a370d70b79d1c44",
"interval": 2,
"qr_data": "bankid.553399f8-8e65-45b5-9b83-d17d2631d88a.0.f6a74ceaafbf31d5274b8b65ffe116c30eace8457870e7aa15beaa7842594efa",
"expires_in": 600,
"autostart_token": "753b0e6b-3342-4fc1-90de-657dc8e39d89"
}
Start polling for below endpoint-
curl -kiSs \
https://www.ident-preprod1.nets.eu/oidc/token \
-H Authorization: Basic <<Base64Enocoded username:password>> \
-d grant_type=urn:openid:params:grant-type:ciba\
-d auth_req_id=5be667afc6624d938a370d70b79d1c44
Upon success, the server will respond with a qr_data -
{
"error": "authorization_pending",
"error_description": "Consent confirmation is still pending",
"qr_data": "bankid.80cc06dc-2686-4d4f-ad0b-73df09d76d80.11.64e6835d7bba6e9389449a4e7fca5e2aa9d56e01bb5c0ac5f014d16317a7d3b1"
}
A QR code generation library can be used to produce the QR code in the preferred size.
A valid JSON format for binding_message is-
{
“transactiontext": “base64encoded (content from merchant)",
“transactiontext_type": “<text/markdown>"
}
TrustID
When starting a CIBA transaction with TrustID, it's optional to specify the end user's identity. This is done by passing the login_hint parameter with the correct data depending on the authentication method. The binding_message parameter accepts JSON format which have data for message which will appear on end user's device, request type, user status etc.
A valid JSON format for binding_message is-
{
"requestType": "<provisioning/authentication>",
"appId": "<appId value>",
"bindingMessage": "<content from merchant>",
"userStatus":"<active/locked >"
}
For more information go to TrustID.
MitID
When starting a CIBA transaction with MitID, it's required to specify the end user's identity. This is done by passing the login_hint parameter with the correct data. login_hint can be a CPR or a UUID. The binding_message parameter is used to specify the text that will appear on the end user's device.
Retrieving the CIBA ID token
curl -kiSs \
https://www.ident-preprod1.nets.eu/oidc/token \
-H "Authorization: Basic <<Base64Enocoded username:password>>" \
-d grant_type=urn:openid:params:grant-type:ciba \
-d auth_req_id=c69597e96f5a4dcc970ec38e5a85a4c3
The following E-Ident providers currently support the CIBA flow:
BankID (NO)
BankID (SE)
Nets ID Verifier
TrustID
MitID
Identification request parameters
The different identification request parameters are divided in these sections:
Mandatory
client_id
|
The customer identifier given upon registration. Often referred to as MID or merchant identifier. This is not the same as the MerchantID.
| |
redirect_uri
| Note: Several redirect_uri URLs can be registered in the configuration. This means that you can use the same configuration for several test environments or production environments. | Customer redirect uri as registered in E-Ident.
|
response_type
| OAuth 2.0 Response Type value that determines the authorization processing flow to be used, including what parameters are returned from the endpoints used. When using the Authorization Code Flow, this value is code.
| code
|
scope
| Scopes are used to retrieve the claims that are grouped in the below table. The optional values are custome scopes in E-Ident. None, one or more can be requested at the same time.
| Mandatory:
openid
Optional:
cert,
email,
organisation,
phone,
profile,
ssn,
address, nemid.pid, agreverifyxx
Space-separated list.
|
Optional
additional_info
|
The additional info parameter can be used by any customer to enter their own information. The parameter value will be returned as it was entered in the corresponding claim in the ID Token or attribute in the SAML assertion.
In addition, the information is added to E-Ident statistics and may be returned to the customers as part of statistics. The last part must be agreed with Nets in each case. |
Format:
[A-Za-z0-9_\-åøæÅØÆ]{0,50}
Max length: 50 characters |
amr_values |
Requested Authentication Method Reference values. This parameter contains 2 values separated by semicolon ( ; ). First value- Space-separated string that specifies the "amr" values that the Authorization Server is being requested to use for processing this Authentication Request, with the values appearing in order of preference. The authentication methods used for the authentication performed are returned as the amr Claim Value. This parameter is equivalent to the forcepkivendor parameter of SAML identification. Second value- Comma-separated string, this will give access to control the authentication method for a specific identification. The actual used authentication method will be returned in the amr claim/attribute.
| First valuee:-
One or more of:
[no_bankid, no_bidmob, no_buypass, mitid, mitid:mitid_erhverv, se_bankid, se_bankid:mobile, fi_tupas, passport_reader/ id_verifier, mobile_id, smart_id, verimi, verimi:idcard, be_cardreader, AusweisApp]
Second value:-
One or more of:
[urn:bankid:bid, urn:bankid:bis, loa.dipp.default, loa.dipp.2fa]
|
|
code_challenge
| The code_challenge is created by If it is not possible to do the above transformation, the code_challenge may be set to the code_verifier value. |
code_challenge_method
| This parameter specifies the method used for the code_challenge parameter. If the parameter is not sent in the request, Nets will assign plain as the default value. | Optional parameter in PKCE flow.
|
code_verifier
| The code_verifier should be a high-entropy cryptographic random string.
| Format: [A-Za-zO-9-._~] Min length: 43 char Max length: 128 char Mandatory in PKCE flow.
|
| deflect | Where the redirect_uri should be opened. Options are to keep it in iframe (_self) or take over the page (_top). |
Valid values: [_top, _self]
Default: _top
|
| id_token_hint | ID Token parameter for prompt=none |
|
| max_age | Maximum Authentication Age. Specifies the allowable elapsed time in seconds since the last time the end user was actively authenticated. If the elapsed time is greater than this value, then the customer should attempt to actively re-authenticate the end user. When max_age is used, the ID Token returned should include an auth_time Claim Value. | Integer value Example: 600 for 10 minutes |
nonce
| String value used to associate a client session with an ID Token, and to mitigate replay attacks. The value is passed through unmodified from the authentication request to the ID Token. Sufficient entropy must be present in the nonce values used to prevent attackers from guessing values.
| Unique random value Max lenght: 500 bytes (UTF-8)
|
| style |
A customer with a specific typographic, layout, or colour scheme can provide a URL to a CSS style sheet. If provided, the given style sheet will be used when rendering web pages in a browser.
Note: style is ignored if the wi parameter is set to “n” or not set at all.
| Format: URL
Range: only URLs to trusted domains are allowed by E-Ident.
Trusted domains are a part of the customer configuration setup.
This parameter overrides the URL issued to E-Ident during configuration. |
| ui_locales |
The language used to provide user with information during identification. If not provided, then E-Ident uses the language specified by the web browser.
If no supported languages are available in the browser, or the parameter, then English is used by default. |
Supported language codes:
[nb-NO | nn-NO | en-GB | da-DK | sv-SE | fi-FI | sv-FI] |
wi
|
The wi parameter is used to indicate that the user interface shall be embedded UI.
Note: The wi parameter may also be set to n to indicate standalone UI. However, as this is default UI option it is not necessary to use the wi parameter. | Valid values: [n|r]
|
Mapping of eID to amr_values parameter:
Optional eID specific parameters
aal_value
| Specifies the requested Authentication Assurance Level. |
One of: [ low | substantial | high ] | MitID DK
|
action_context
| Specifies the action context for identification
|
One of:
[LOG_ON | APPROVE | CONFIRM |ACCEPT | SIGN]
| MitID DK (Currently supported)
|
acr_values
| Used to set the level of assurance for the identification
| Valid values:
urn:eident:acrp:level:low
urn:eident:acrp:level:substantial
urn:eident:acrp:level:high
| BankID (NO), BankID (SE), MitID DK, Finnish Bank ID (FI), Mobile-ID, Nets One Time Code, Buypass, Verimi, Nets ID Verifier
|
amr_values
| Used to set the authentication method for the identification
| Valid values: See the eID specific page
|
|
autostart
| Will skip the first page and automatically select BankID on this computer / device. A link will be shown to open the BankID app.
| | BankID (SE)
|
| celnr8 |
8-digit mobile/cell number for BankID on mobile (NO). | Encoding: Base64 | BankID on mobile (NO) |
dob6
|
6-digit date of birth for BankID on mobile (NO). | Encoding: Base64 | BankID on mobile (NO) |
eident_context |
Finnish BankID (FI) Service provider name
BankID (SE) Text displayed in the app
| Base64 encoded JSON.
see eID specific page | Finnish BankID (FI) - Danske Bank, Ålandsbanken, S-Pankki, Aktia
BankID (SE)
|
| forcebank |
amr_values=fi_tupas.
If the parameter is not used, a list of all the Tu-pas banks configured on the customer site will be displayed. | One of:
nordea |
opbank |
danske |
handelsbanken |
aland |
sbank |
aktia |
popbank |
savingsbank |
omasp | mobileid | Finnish Bank ID (FI) |
loa_value
| Specifies the requested Level of Assurance. |
One of: [ low | substantial | high ] | MitID DK |
login_hint
| A pre-selected user ID to improve user experience and reduce number of steps for a user.
| See login_hint description on the eID specific pages.
| Applicable for these: BankID (NO), BankID (SE), MitID (DK) Mobiilivarmenne (FI), Mobile-ID, Smart-ID and Verimi |
| mobileid_display_te-xt_format |
This parameter indicates the format to use for the display text. GSM-7 is default. UCS-2 supports all Cyrrillic characters.
|
Valid values: - UCS-2: 20 characters
- GSM-7: 40 characters (default)
|
Mobile-ID
|
| presetid | A pre-selected user ID to improve user experience and reduce number of steps for a user. | See presetid description on the eID specific pages. | Applicable for these: BankID (NO), BankID (SE), MitID DK Mobiilivarmenne (FI) and Verimi |
| reference_text |
Reference text displayed during MitID identification. The text is displayed in the MitID client or in the MitID app.
| All characters allowed except:
Max length: 130 |
| |
smartid_allowed-InteractionsOrderType
|
This parameter can be used to decide which text to display to the user and it may give him possibilities to choice a verification code.
| Valid values:
See the eID specific page.
|
Smart-ID
|
smartid_displayText60
|
Text to be displayed in the Smart-ID user app.
| Max length:
60 characters
|
Smart-ID
|
smartid_displayText200
|
Text to be displayed in the Smart-ID user app.
| th:
200 characters
|
Smart-ID
|
| transactiontext | Transaction text -
BankID security app/mobile app - displayed in the app
- Mobile-ID - displayed on the phone
- MitID - displayed in the user dialouge at the MitID broker
- AusweisApp – displayed to the user on the Ausweis app
| Characters
Max length:
BankID SE: 600 characters Mobile-ID: UCS-2 20 characters GSM-7 40 characters AusweisApp: 1800 characters
|
|
|
transactiontext_type
| The type of the transaction text.
| Valid values: [html | text]
|
MitID (DK)
|
|
|
ntdr-app-doclist
| Specifies weather to display document selection page in the mobile app for document scan i.e to select passport or ID card.
|
Values:
[true | false]
Default value is false.
| Nets ID Verifier
|
|
|
ntdr-doc-issuers
| Specifies which issuing countries' documents to allow during ID verification. This parameter specifies a list of allowed document issuers. It accepts a pattern of three-letter (ISO 3166) country codes. If no list is provided, no document issuer checks are enforced.
| Format: [A-Za-z] Example: MYT,KNA,SWZ Max length: 3 char | Nets ID Verifier
|
ntdr-doc-types
| Specifies a list of accepted document types. It accepts a pattern of one or two letter document codes.
Important: Please note that document codes are defined by the issuing authority and there is no fixed standard. If no list is provided, no document type checks are enforced.
Example for passports:
ntdr-doc-types=P
| Format: [A-Za-z] Min length: 1 char Max length: 2 char
Supported document types: Passport, ID Card
| Nets ID Verifier
|
ntdr-expiry-grace
| Enforces document validity check, if this parameter is set. If it is not set, then document validity check will be skipped returning successful identification response for expired documents, and the document validity check will be the merchant's responsibility.
Example: If this parameter is set to 0, then the ID token will have failure response for expired documents. If this parameter is set to negative value, say -5, then the ID token will have failure response for the documents that are about to expire in 5 days or less from the current date. If this parameter is set to positive value, say 5, then the ID token will have failure response for the documents that have expired 5 days ago or more from the current date.
Important: Irrespective of this parameter's value, the App will allow expired documents to be used successfully by the users, but the ID token will indicate whether the identification is successful, or a failure based on this parameter's value.
| Example: 30
| Nets ID Verifier
|
ntdr-info
| Toggle if info page to download Nets ID Verifier app should be shown.
| Values: true | false
| Nets ID Verifier
|
|
ntdr-facematch-min
| Indicates the minimum acceptable face match level for successful authentication.
| 0-8
| Nets ID Verifier
| |
ntdr-doc-types
| Allowed document types. Accepts multiple values with comma separation.
| I, P, D, V (I – ID Card, P – Passport Booklet, D – Driver’s License, V – Viza/Crew credentials)
| Nets ID Verifier
| |
ntdr-app-doclist
| Indicates whether to display document type selection page in mobile app for the user to select.
| true | false
| Nets ID Verifier
| |
ntdr-doc-issuers
| Restricts the document issuer countries to the given list.
| NOR for Norway, SWE for Sweden, etc (ISO-3166-1 alpha-3 cods)
| Nets ID Verifier
| |
CIBA specific parameters
| amr_values | Requested Authentication Method Reference values. Can only contain a single value for CIBA transactions. | One of:
[no_bidmob,
se_bankid, se_bankid:mobile,
passport_reader/id_verifier,trustid,mitid]
|
Signed request
E-Ident supports Signed Request Object (Signed JWT) in OIDC requests. Both request and
request_uri parameters are supported as specified by the OIDC standard. E-Ident will do a RSA signature verification to make sure that the Request Object is signed by the expected E-Ident customer by using a public key associated with the
client_id.
The customer will need to provide Nets with one of the following options:
- A URL to a JWKS endpoint where Nets can look up a public key for signing purposes. It is optional to also provide a key id. Otherwise the first public key in the response from the endpoint will be used.
- The RSA key members and the key type in JSON format.
If using the
request_uri option, the request uri will have to be registered by Nets.
ID Token
The ID Token is a JSON Web Token (JWT) and is either signed or signed-then-encrypted. The default is signed. For more information on encryption, see
ID Token Encryption section.
The ID Token signature should be validated using the public key that is mentioned in the kid element in JWT header. The corresponding key can be looked up from E-Ident’s JWKS endpoint.
The ID Token is valid for 15 minutes. Successive token requests with the same authorization code (code) will result in error and invalidation of previously accessed tokens.
scope parameter value from the identification request. The
openid value must always be used while
cert,
profile and
ssn is optional. All ID Token claims are listed here, sorted by the
scope value. See examples in
Step 3 on how to retrieve an ID Token.
openid
aal
|
Authentication Assurance Level |
One of https://data.gov.dk/concept/core/nsis/Low https://data.gov.dk/concept/core/nsis/Substantial https://data.gov.dk/concept/core/nsis/High
Applicable eID: MitID (DK) |
action_context
| Specifies the action context for identification
|
One of: [LOG_ON | APPROVE | CONFIRM |ACCEPT | SIGN]
Applicable eID: MitID (DK) (Currently supported)
|
| acr | The level of assurance for the specific identification. | Possible values are listed on the eID pages, which will be one of: [ urn:eident:cert:eidas:high| urn:eident:cert:eidas:substantial| urn:eident:cert:eidas:low ]
|
| additional_info |
The value of the additional info parameter if used. |
|
| amr | Auth Method Ref. JSON array of strings that are identifiers for authentication methods used in the authentication. In E-Ident, this is the eID type used in the identification. | One of:
[no_bankid | no_bidmob | no_buypass | mitid | se_bankid | fi_tupas | fi_mobiilivarmenne | passport_reader/id_verifier | email | idcard | smart_id | mobile_id ]
|
aud
| Audience(s) that this ID Token is intended for. | The unique customer "MID" value. |
auth_time
| Time when the end user identification occurred. | The value is a JSON number representing the number of seconds from 1970-01-01T0:0:0Z as measured in UTC until the date/time. |
bp_pid
| Personal identifier of Buypass user
| Applicable eID: Buypass
|
bp_id_sub
| Unique identifier from Buypass
| Applicable eID:
Buypass
|
card_number
| Card number of the end user
| Applicable eID:
Belgian eID (BE)
|
card_expiry_date
| Expiry date of the end user's card
| Applicable eID:
Beligan eID (BE)
|
exp
| Expiration time on or after which the ID Token must not be accepted for processing. | The value is a JSON number representing the number of seconds from 1970-01-01T0:0:0Z as measured in UTC until the date/time. |
| fi_trx_code | Unique but transient anonymous identifier for the end user. Remains the same in identity token and UserInfo responses during one authentication session, but is different in subsequent authentications of the same user. | Applicable eID: Mobiilivarmenne (FI) |
| fi_tupas_bank | The user’s bank used in the identification process. | One of: [nordea |
opbank |
danske |
handelsbanken |
aland |
sbank |
aktia |
popbank |
savingsbank |
omasp | mobileid] Applicable eID: Finnish Bank ID (FI) |
| fi_tupas_pid | A fixed identifier for the user set in the E-Ident / FTN service. | Applicable eID:
Finnish Bank ID (FI) |
| ial |
Identity Assurance Level |
One of https://data.gov.dk/concept/core/nsis/Low https://data.gov.dk/concept/core/nsis/Substantial https://data.gov.dk/concept/core/nsis/High
Applicable eID: MitID (DK) |
| iat | Time at which the JWT was issued. | The value is a JSON number representing the number of seconds from 1970-01-01T0:0:0Z as measured in UTC until the date/time. |
identity_type
| Type of identification
| Possible values are:
Professional indicates Erhverv user
Applicable eID:
MitID (DK)
|
| iss | Issuer Identifier for the Issuer of the response. E-Ident issuer URI | |
| loa | |
One of https://data.gov.dk/concept/core/nsis/Low https://data.gov.dk/concept/core/nsis/Substantial https://data.gov.dk/concept/core/nsis/High
Applicable eID: MitID (DK) |
| mitid_amr |
The list of authenticators used to achieve the resulting level of assurance for a MitID identification. |
Possible values for MitID are:
password
code_token
code_reader
code_app code_app_enchanced u2f_token
Possible values for MitID Erhverv are:
mitid:password
mitid:code_token mitid:code_reader mitid:code_app mitid:code_app_enchanced mitid:u2f_token
Applicable eID: MitID (DK) |
mitid.uuid
| Unique identifier for MitID. | Applicable eID: MitID (DK) |
mobileid_pid
| Unique identifier of user in the E-Ident service.
| Applicable eID:
Mobile-ID
|
nemlogin.ial
| Identity Assurance Level for Erhverv user
|
One of https://data.gov.dk/concept/core/nsis/Low https://data.gov.dk/concept/core/nsis/Substantial https://data.gov.dk/concept/core/nsis/High
Applicable eID: MitID (DK) |
nemlogin.persistent
_professional_id
| MitID Erhverv’s Global UUID/ID from EIA
| Applicable eID:
MitID (DK)
|
| no_bid_pid | Norwegian BankID personal identifier. | Applicable eIDs: BankID (NO) and BankID on mobile (NO) |
| nonce | String value used to associate a Client session with an ID Token, and to mitigate replay attacks. The value is passed through unmodified from the Authentication Request to the ID Token. | |
| notafter | Certificate validity end time. | Applicable eIDs:
BankID (NO), BankID on mobile (NO), BankID (SE)
|
| notbefore | Certificate validity begin time. | Applicable eIDs:
BankID (NO), BankID on mobile (NO), BankID (SE)
|
| phone_number | 8-digit mobile/cell number (provided by merchant or user) | Applicable eID:
BankID on mobile (NO) |
pid
| Personal identifier. Content will vary from eID to eID. | See possible values in "Information about end user" section for each eID. |
reference_text
| Reference text from
MitID and/or Erhverv transactions
| Applicable eID:
MitID (DK)
|
| se_bid_securitylevel | Swedish BankID security level | Applicable eID: BankID (SE)
|
smartid_inter-action_flow_used
|
This value returns information about the type of Smart-ID interaction flow that was used. This can be one of:
- displayTextAndPIN
- verificationCodeChoice
- confirmationMessage
- confirmationMessageAndVerificationCodeChoice
| Applicable eID:
Smart-ID
|
smartid_pid
| Unique identifier of user in the E-Ident service.
| Applicable eID:
Smart-ID
|
sub
| Subject Identifier. | A string in the format "eID type:ID"
|
transaction_text
| The transaction text sent through E-Ident is returned in this claim.
| Applicable eID:
BankID (SE), Mobile-ID and MitID (DK)
|
transaction_te-xt_sha256
| Base64 encoded SHA256 digest of the MitID transactiontext identity provider parameter.
| Applicable eID:
MitID (DK)
|
transaction_te-xt_type
| The type of the transaction text. This may either be html or text.
| Applicable eID:
MitID (DK)
|
Jti
| JWT ID
| The unique transaction ID
|
authentication_result
| Authentication result
| Applicable eID:
Nets ID Verifier
|
chip_clone_detection
| Status of chip clone detection
| Applicable eID:
Nets ID Verifier
|
facematch_level
| Face match level
| Applicable eID:
Nets ID Veriifer
|
issuing_country
| Issuing country (country code)
| Applicable eID:
Nets ID Verifier
|
interpreted_issuing_country
| Issuing country (country name)
| Applicable eID:
Nets ID Verifier
|
cert
| c | The country associated with the end user's eID. | Applicable eID:
All (if available) |
| certificate | The end user's certificate. | Applicable eID:
BankID (NO), BankID on mobile (NO) and BankID (SE) |
| certpolicyoid | The certificate policy of the end user's certificate. | Applicable eID: All (if available) |
| cn | The common name from the end user's certificate. | Applicable eID:
All (if available) |
| dn | The distinguished name from the end user's certificate. | Applicable eID:
All (if available)
|
email
| email | The end user's e-mail address. | Applicable eIDs: BankID (NO), BankID on mobile (NO) and Verimi.
|
nemid.pid
nemid.pid
| If the user has a NemID identity, this will be the user's unique NemID PID value. | Applicable eIDs: MitID
|
organisation
| authorized_to_represent |
The organisation number (Danish CVR number) the user has selected and is authorised to represent. The user can select a company when using the Private MitID - on behalf of companies functions. | Applicable eID:
MitID (DK) |
| organisation_name |
Private MitID: The name of the organisation the user logs in on behalf of. For Finnish Bank ID:
The organisation name connected to the user's legal person ID. | Applicable eID:
MitID (DK) and Finnish Bank ID (FI) |
| organisation_number |
For MitID:
The organisation number received when using the Private MitID - on behalf of companies function. For Finnish Bank ID:
The organisation number (VAT) connected to the user's legal person ID. | Applicable eID:
MitID (DK) and Finnish Bank ID (FI) |
phone
| phone_number | The end user's phone number. | Applicable eIDs: BankID (NO), BankID on mobile (NO), Mobiilivarmenne (FI) and Verimi |
profile
| birthdate | Date of birth in the format DD.MM.YYYY | Applicable eID: BankID (NO), BankID on mobile (NO), Finnish Bank ID (FI) and Mobiilivarmenne (FI), AusweisApp
|
| family_name | The end user's surname | Applicable eID:
All (if available) |
| given_name | The end user's given name. | Applicable eID:
All (if available) |
| name | The end user's full name.
| Applicable eID:
All (if available)
|
nemlogin.age
| Age of Erhverv user
|
Applicable eID:
MitID (DK)
|
nemlogin.auth_to_repr
| CVR number of the Organisation for which the MitID user is authorized to represent.
|
Applicable eID:
MitID DK)
|
nemlogin.cpr_uuid
| Unique ID for Erhverv user
|
Applicable eID:
MitID (DK) |
nemlogin.cvr
| Company CVR for Erhverv user
|
Applicable eID:
MitID (DK |
nemlogin.date_of_birth
| Date of birth for Erhverv user
|
Applicable eID:
MitID (DK)
|
nemlogin.email
| Email address for Erhverv user |
Applicable eID:
MitID (DK)
|
nemlogin.family_name
| Family name for Erhverv user |
Applicable eID:
MitID (DK)
|
nemlogin.given_name
| Given name for Erhverv user |
Applicable eID:
MitID (DK)
|
nemlogin.name
| Full name of Erhverv user
|
Applicable eID:
MitID (DK)
|
nemlogin.nemid.rid
| Employee certificate RID from NemID migration (or assigned)
|
Applicable eID:
MitID (DK)
|
nemlogin.org_name
| Company name for Erhverv user |
Applicable eID:
MitID (DK)
|
nemlogin.p_number
| Company P number for Erhverv user
|
Applicable eID:
MitID (DK)
|
nemlogin.persistent
_professional_id
| MitID Erhverv’s Global UUID/ID from EIA
|
Applicable eID:
MitID (DK)
|
nemlogin.se_number
| Company SE number for Erhverv user |
Applicable eID:
MitID (DK)
|
auth_files_url
| A URL to download authentication files. Read more about the authentication files.
| Applicable eID:
Nets ID Verifier
|
document_number
| The Document Number
| Applicable eID:
Verimi IDCard
Nets ID Verifier
|
document_type
| The Document Type
| Applicable eID:
Verimi IDCard
Nets ID Verifier, AusweisApp
|
place_of_birth
| Place of Birth | Applicable eID: Verimi IDCard Nets ID Verifier, AusweisApp
|
date_of_expiry
| Date of Expiry of the document | Applicable eID:
Verimi IDCard Nets ID Verifier, AusweisApp
|
citizenship
| Citizenship of the end user
| Applicable eID: Verimi IDCard
|
issue_date
| The Document issue date
| Applicable eID: Verimi IDCard
|
issuing_authority
| The Document issuing authority
| Applicable eID:
Verimi IDCard
|
verification_method
| Verification Method | Applicable eID:
Verimi IDCard
|
verification_date
| Date of verification | Applicable eID: Verimi IDCard
|
gender
| Gender
| Applicable eID:
Nets ID Verifier
|
nationality
| Nationality (country code)
| Applicable eID:
Nets ID Verifier, AusweisApp
|
interpreted_nationality
| Nationality (country name)
| Applicable eID:
Nets ID Verifier
|
primary_identifier
| Predominant componet of
the name of the holder
| Applicable eID:
Nets ID Verifier
|
secondary_identifier
| Secondary component of
the name of the holder
| Applicable eID
Nets ID Verifier
|
ssn
dk_ssn
| Danish SSN | Applicable eID: MitID (DK) |
| fi_ssn |
End user's Finnish personal identity code (henkilötunnus). | Applicable eIDs: Finnish Bank ID (FI) and Mobiilivarmenne |
| fi_satu |
Finnish unique identification number (sähköinen asiointitunnus). | Application eID: Finnish Bank ID (FI) |
no_ssn
| Norwegian SSN | Applicable eID: BankID (NO), BankID on mobile (NO) and Buypass
|
| se_ssn | Swedish SSN | Applicable eID: BankID (SE) |
smartid_document_number
| See description at
Smart-ID page.
| Applicable eID:
Smart-ID
|
ssn
| Social security number / National identifier | Applicable eIDs: BankID (NO), BankID on mobile (NO), Buypass (NO), MitID (DK), BankID (SE), Finnish Bank IDs (FI) and Mobiilivarmenne. |
address
| address | The end user's address | Applicable eIDs: BankID (NO), BankID on mobile (NO), Mobiilivarmenne (FI) and Verimi, AusweisApp
|
ageverifyxx
age_verified
| This claims tells if the age has been verified or not
| One off: true | false | inconclusive Applicable eIDs: Finnish BankID (FI)
|
ID Token sample
{
"sub" : "mitid:PID:xx-xx-xx-xx",
"dk_ssn" : "xx",
"amr" : "mitid",
"mitid.uuid" : "xx-xx-xx-xx",
"iss" : "https://www-ident-test.nets.no/oidc",
"dn" : "CN=Frida Jørgensen",
"pid" : "PID:xx-xx-xx-xx",
"nonce" : "nonce07/06/2023",
"aal" : "https://data.gov.dk/concept/core/nsis/High",
"ssn" : "xx",
"aud" : "MER2",
"ial" : "https://data.gov.dk/concept/core/nsis/High",
"mitid_amr" : [ "code_app" ],
"exp" : 1686117229,
"identity_type" : "private",
"iat" : 1686116329,
"jti" : "xx-xx-xx-xx-xx",
"loa" : "https://data.gov.dk/concept/core/nsis/High"
}
ID Token encryption
Customers can request Nets to encrypt all ID Tokens. The ID Token will be encrypted using RSA-OAEP-256 and AES, as described by RFC 7516. JWE Compact serialization is used and the encryption is done after signing, which means that the customer needs to decrypt the ID Token before being able to validate the signature.
The customer will need to provide Nets with one of the following options:
- A URL to a JWKS endpoint where Nets can look up a public key for encryption purposes. It is optional to also provide a key id. Otherwise the first public key in the response from the endpoint will be used.
- The RSA key members and the key type in JSON format.
Note: The use of encrypted ID Token is required for Finnish Trust Network customers offering identification with Finnish Bank IDs and Mobiilivarmenne.
Get in touch with support for more details.
OIDC discovery URL
OIDC discovery request has to be made to get the token_endpoint and jwks_uri. This can be done programmatically or manually to get the token_endpoint uri and jwks_uri.
The OIDC discovery URL:
- Customer test:
https://www.ident-preprod1.nets.eu/oidc/.well-known/openid-configuration
- Production:
https://www.e-ident.nets.eu/oidc/.well-known/openid-configuration
OIDC UserInfo endpoint
The UserInfo endpoint returns claims about the authenticated user,
including some claims not available in the ID token. Accessing this endpoint requires an access token. This token is returned together with the ID token. The access token shouldn't be expired to get the authentication data. The endpoint response will be in JSON format.
For SAML protocol, the access token will be available in the SAML response.
The OIDC userinfo endpoint URL:
- Customer test: https://www.ident-preprod1.nets.eu/oidc/userinfo
- Production:
https://www.e-ident.nets.eu/oidc/userinfo
Requesting authentication data from UserInfo endpoint
curl https://www.ident-preprod1.nets.eu/oidc/userinfo -H "Authorization: Bearer <<access token>>"
Sample UserInfo endpoint response
{
"sub" : "se_bankid:xxxxxxxxxxxx",
"user_signature" : "<<user_signature>>",
"user_cert_ocsp" : "<<user_cert_ocsp>>",
"notbefore" : "20210112230000",
"amr" : ["se_bankid"],
"notafter" : "20230113225959",
"iss" : "https:\/\/www.ident-preprod1.nets.eu\/oidc",
"given_name" : "Test",
"nonce" : "nonce06\/09\/2021",
"auth_device_ip" : "xxx.xxx.xxx.xx",
"ssn":"xxxxxxxxxxxx",
"access_token" : "QzLCDFodNn0y4XdGY2AVKRdDxY2JFiHLDZm0bz8aV-E",
"aud" : "Test merchant",
"se_ssn" : "xxxxxxxxxxxx",
"name" : "Test Testesen",
"exp" : 1630915131,
"iat" : 1630914231,
"family_name" : "Testesen",
"jti" : "278b78056a8349f68be8679d7f908159"
}
Userinfo endpoint claims
The userinfo endpoint may return these claims in addition to the claims in the ID Token.
picture
| Picture of the end user as read from the card
| Currently supported for
|
user_cert_ocsp
| The OCSP response returned from the eID when validating the authentication. | Currently supported for: |
user_signature
| The signature returned from the eID during the authentication. | Currently supported for: |
verification_info
| Proof of authentication as provided by the electronic ID provider.
| Currently supported for:
|
access_token
| Credential issued by authorization server for accessing protected APIs
| Supported for all eIDs
|
face_scan_time
| Time when face scan was
completed
| Currently supported for:
|
document_scan_time
| Time when document scan was
completed
| Currenly supported for:
|
transaction_start_time
| Time when the transaction was started
| Currently supported for:
|
transaction_end_time
| Time when the transaction was completed
| Currently supported for:
|
Recommended reading
The OIDC standard is described here:
http://openid.net/connect/
Referenced documentation:
http://openid.net/specs/openid-connect-core-1_0.html
Reference implementations: